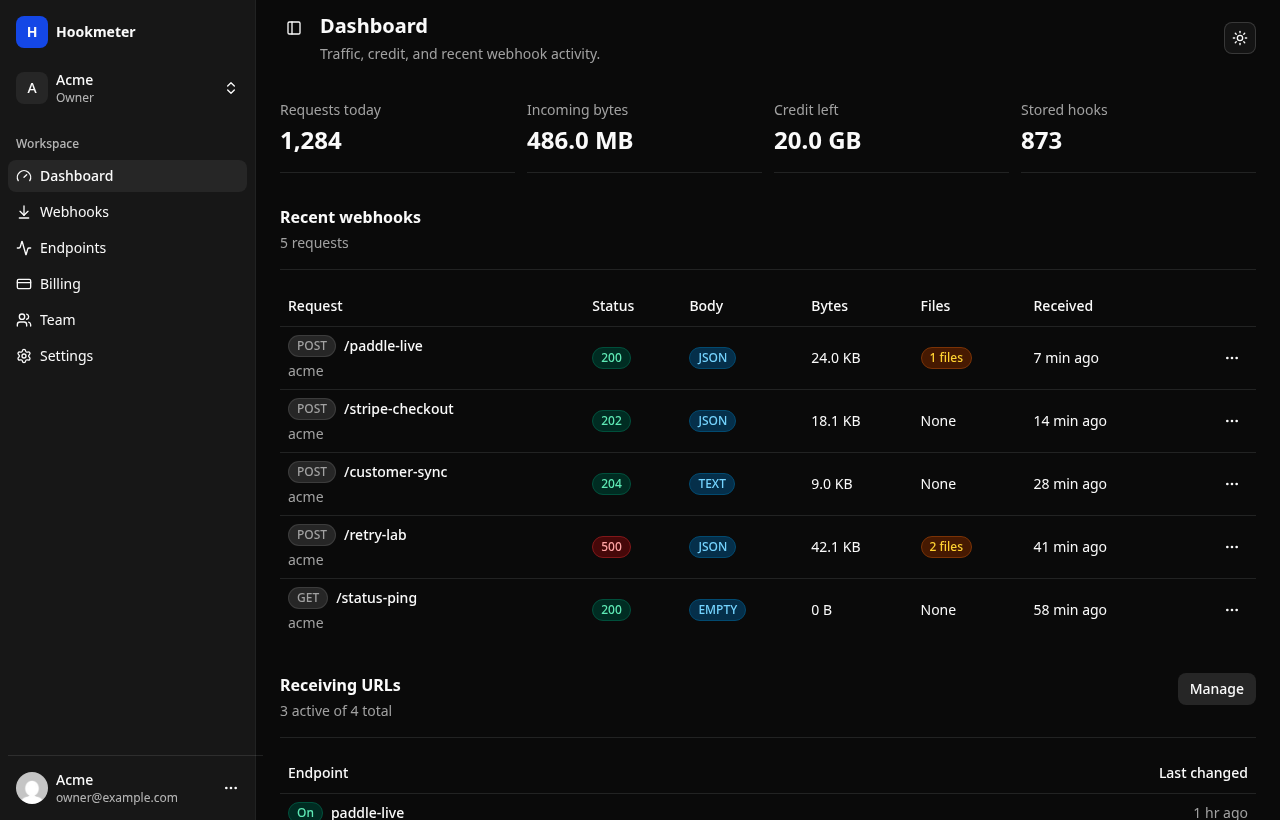
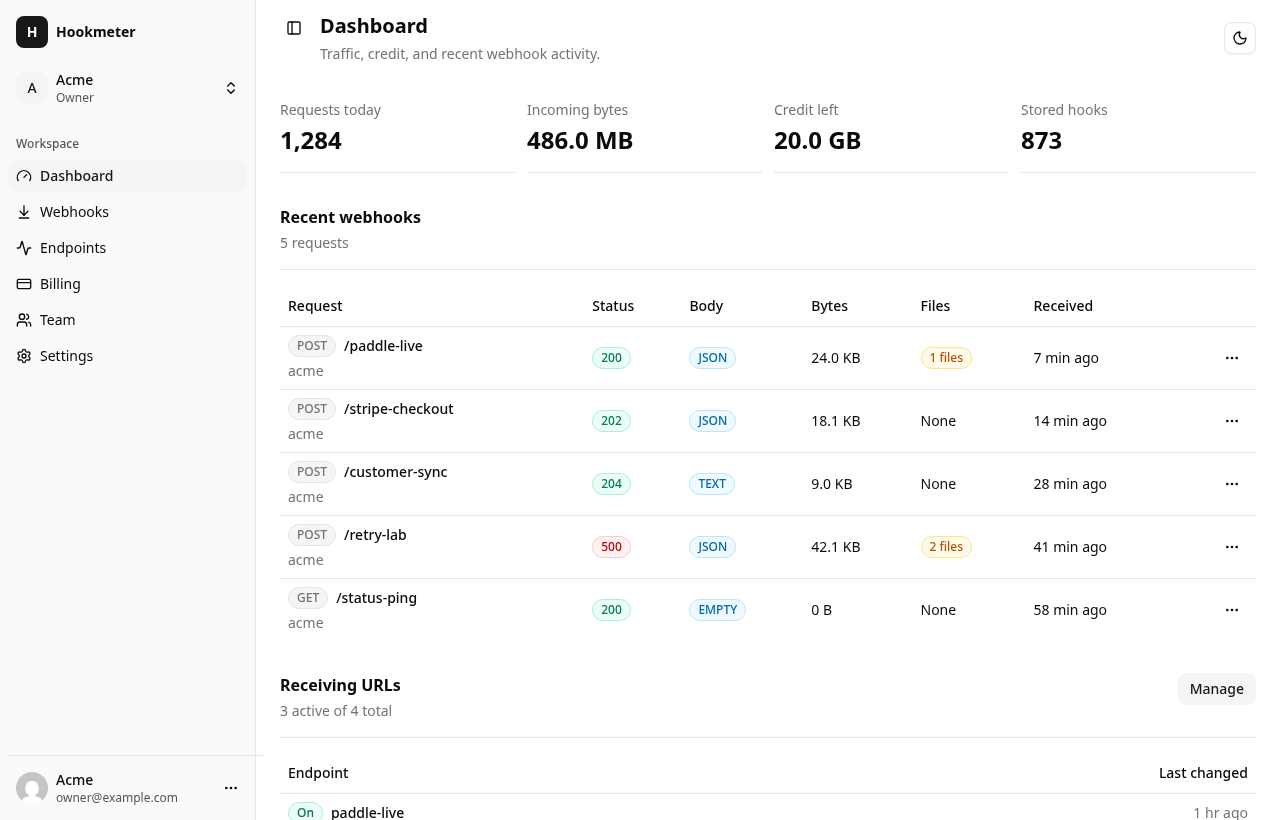
Capture Paddle, Stripe, and billing-provider callbacks while checkout, retries, and subscription state are still in motion.
Receive, inspect, and debug webhooks.
Stable endpoints, full request capture, and shared payload inspection for teams testing payments, automations, and integrations.
Where webhook debugging slows teams down.
SignalBin is built for the messy middle of integration work, when provider callbacks are real but the system around them is still changing.
Give Zapier, Make, n8n, and internal jobs a stable URL while you compare every delivered payload.
Open the exact webhook record behind a failed sync instead of asking engineering to search terminal logs.
Keep provider callbacks separate by product, tenant, or environment without running a local tunnel all day.
From provider callback to shared evidence.
Simple usage model, careful request handling.
Traffic-based pricing for webhook visibility.
Start testing quickly, then scale as your team sends more webhook traffic.
Controls for sensitive webhook traffic.
Endpoint access, payload safeguards, workspace membership, and operational checks are visible and intentional.
Common questions before sending the first request.
Is SignalBin a local tunnel?
No. SignalBin gives you stable hosted receiving URLs and stores webhook history so teammates can inspect requests later.
Can I separate providers or environments?
Yes. Create endpoints per provider, product, tenant, or environment, then filter webhook history by endpoint.
What can I inspect?
Webhook detail pages show method, status, headers, detected body type, raw payload, received time, bytes, and attached files.
How does billing work?
Usage is based on received webhook traffic. The billing screen shows available credit, traffic packs, ledger entries, and purchases.
Start with one endpoint.
Send a request, open the payload, and see exactly what your provider delivered.